Licences & Software
All Microsoft licences from a single source – simple, secure and reliable.

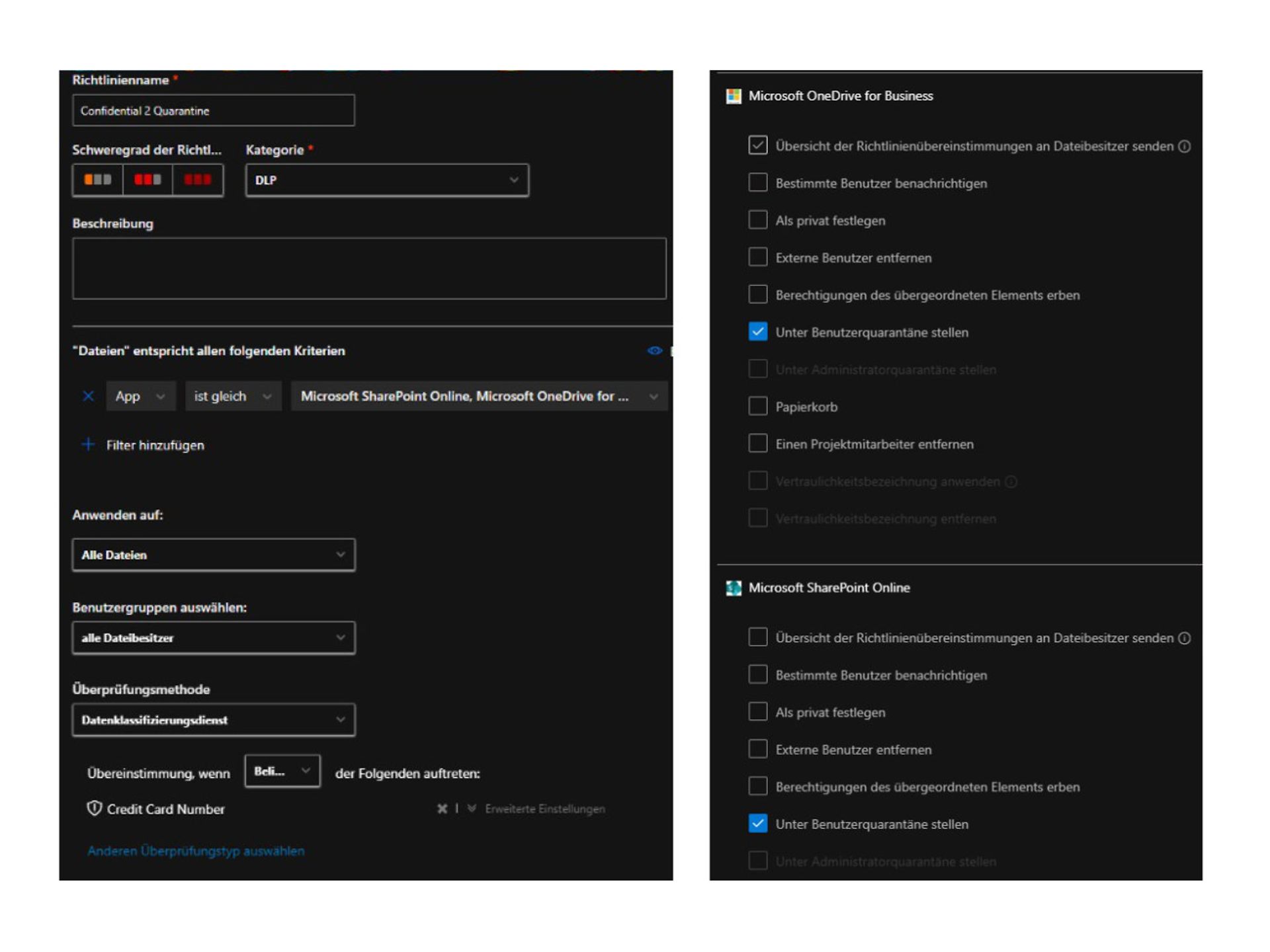
MDCA can automatically detect sensitive files in OneDrive/SharePoint and, for example, quarantine or delete them.
In today's cloud-centric working world, protecting sensitive information is crucial. Companies are increasingly turning to Microsoft Purview Information Protection to classify and protect data.
However, such functions are usually not configured or are inadequately configured at the start, meaning that sensitive data finds its way into OneDrive or SharePoint, even though it may not be stored in cloud storage for regulatory reasons or similar.
In this article, I will show you how to use Microsoft Defender for Cloud Apps (MDCA) to automatically detect documents and take appropriate action, such as quarantining or deleting them.
Before we begin, the following components should be set up:
Probably the most difficult point – reliable recognition of documents in bulk. We have the following options:
In the Security Admin Portal:
A user accidentally saves a file with recognisable content to their OneDrive. MDCA recognises the file, triggers the policy and automatically moves it to quarantine. The user receives a notification with a reference to the policy.
Actions performed by file policies can be tracked in the governance log in the MDCA.
Security Admin Centre > Cloud Apps > Governance Log
The combination of Defender for Cloud Apps and various detection methods, such as Sensitive Info Types + Co, offers a powerful way to detect sensitive data. With appropriate policies in place, violations can be automatically detected and remedied before they become a security risk.
Integrating Microsoft Data Classification Services - Microsoft Defender for Cloud Apps | Microsoft Learn
Working with the RegEx engine - Microsoft Defender for Cloud App | Microsoft Learn
Creating a digital document fingerprint - Microsoft Purview | Microsoft Learn
Getting started with trainable classifiers - Microsoft Purview | Microsoft Learn
Modern IT and cloud scenarios place new demands on security, governance and operations. Telekom's consulting services on Microsoft security help you analyse your environment in a structured manner and develop it in a targeted way – from initial classification to concrete implementation.
Start with a no-obligation orientation meeting or a Microsoft 365 Security Assessment and receive clear recommendations for action to improve security.
Do you have questions about Telekom's Microsoft service offering or would you like personal advice? Simply contact our experts without obligation using the consultation form.
All Microsoft licences from a single source – simple, secure and reliable.
übergreifend-Teaser-Telekom-Partner-Lizenzen-Software-Link-CMP
Certified experts support you with tailor-made solutions for your business.
Discover our offer
We are always there for you: quick assistance, personal support – at no extra cost.
Contact
ISG and Microsoft-certified services for maximum security and reliability.
About the Microsoft portfolio

Marcus began working with Microsoft Office 365 in 2014. Since then, he has focused on various projects and supported customers from a wide range of industries. In recent years, Marcus has concentrated on Microsoft security issues.